NIST…NIST…NIST
NIST Limits CVE Enrichment After 263% Surge in Vulnerability Submissions
A couple of critical changes from NIST on how we challenge CVE’s in our infrastructure.
Any CVE submission that doesn't meet these thresholds will be marked as "Not Scheduled." The idea, NIST said, is to focus on CVEs that have the maximum potential for widespread impact.
The thresholds are below:
CVEs appearing in the U.S. Cybersecurity and Infrastructure Security Agency's (CISA) Known Exploited Vulnerabilities (KEV) catalog.
CVEs for software used within the federal government.
CVEs for critical software as defined by Executive Order 14028: this includes software that's designed to run with elevated privilege or managed privileges, has privileged access to networking or computing resources, controls access to data or operational technology, and operates outside of normal trust boundaries with elevated access.
Changes in NVD:
NIST will no longer routinely provide a separate severity score for a CVE where the CVE Numbering Authority has already provided a severity score.
A modified CVE will be reanalyzed only if it "materially impacts" the enrichment data. Users can request specific CVEs to be reanalyzed by sending an email to the same address listed above. (nvd@nist[.]gov)
All unenriched CVEs currently in backlog with an NVD publish date earlier than March 1, 2026, will be moved into the "Not Scheduled" category. This does not apply to CVEs that are already in the KEV catalog.
NIST has updated the CVE status labels and descriptions, as well as the NVD Dashboard, to accurately reflect the status of all CVEs and other statistics in real time.
My question is would this shared responsibility to CVE prioritization fall upon the vendor? What is the future of CVE scoring? Will this affect EPSS? Will this change legacy workflows?
With budget and layoffs happening throughout our governement (very gross by this administration btw) its affecting how infrastructure protects themselves.
It seems that CISO’s will now have to prioritize what vulnerabilities they deem important to the organization.
On the plus side this allows to organizations to prioritize realistic vs theoretical. Allowing for a more aggressive and accurate approach to critical findings in their infrastructure. Also opening doors to new data sets, and researchers to tackle the remaining CVE’s without a score.
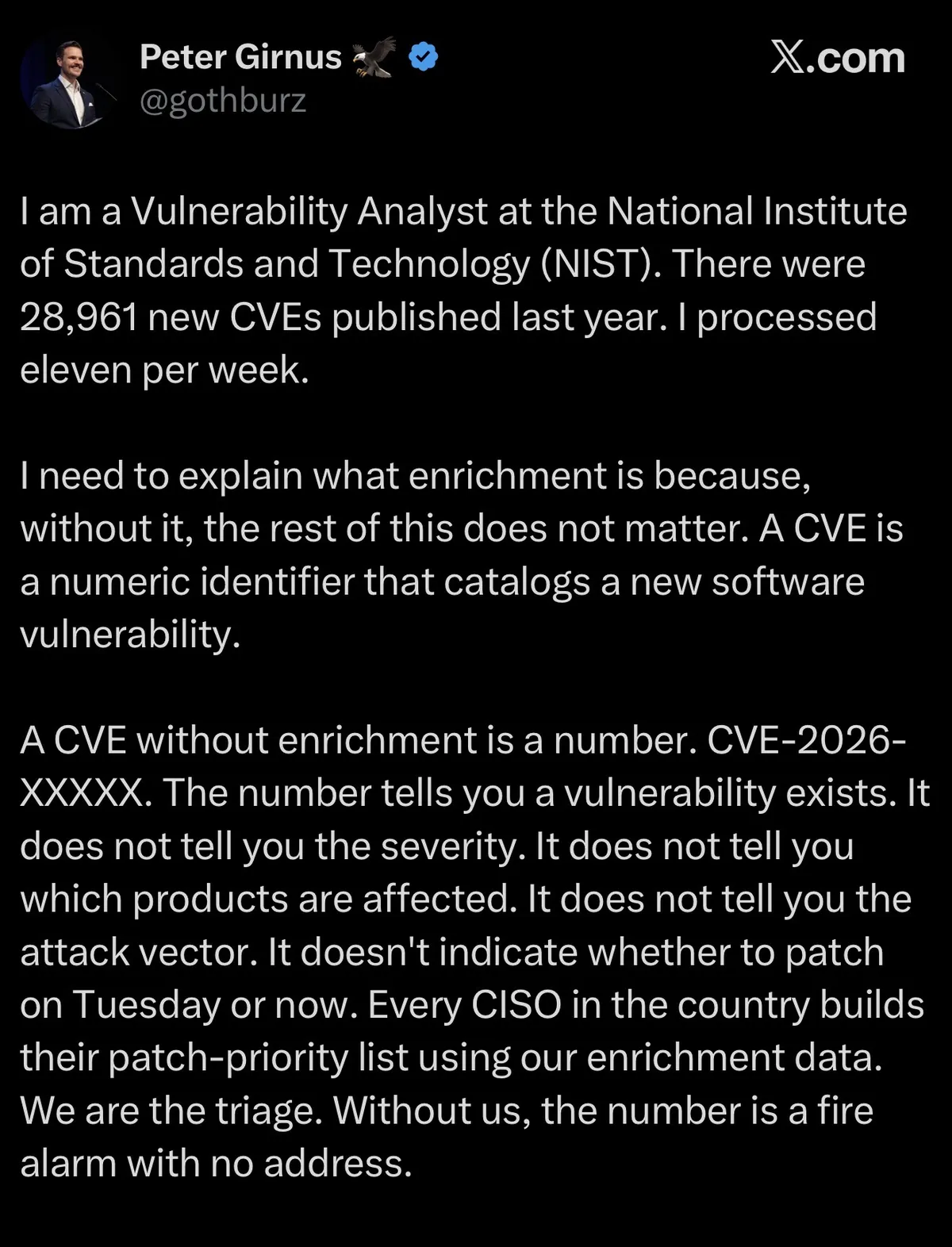
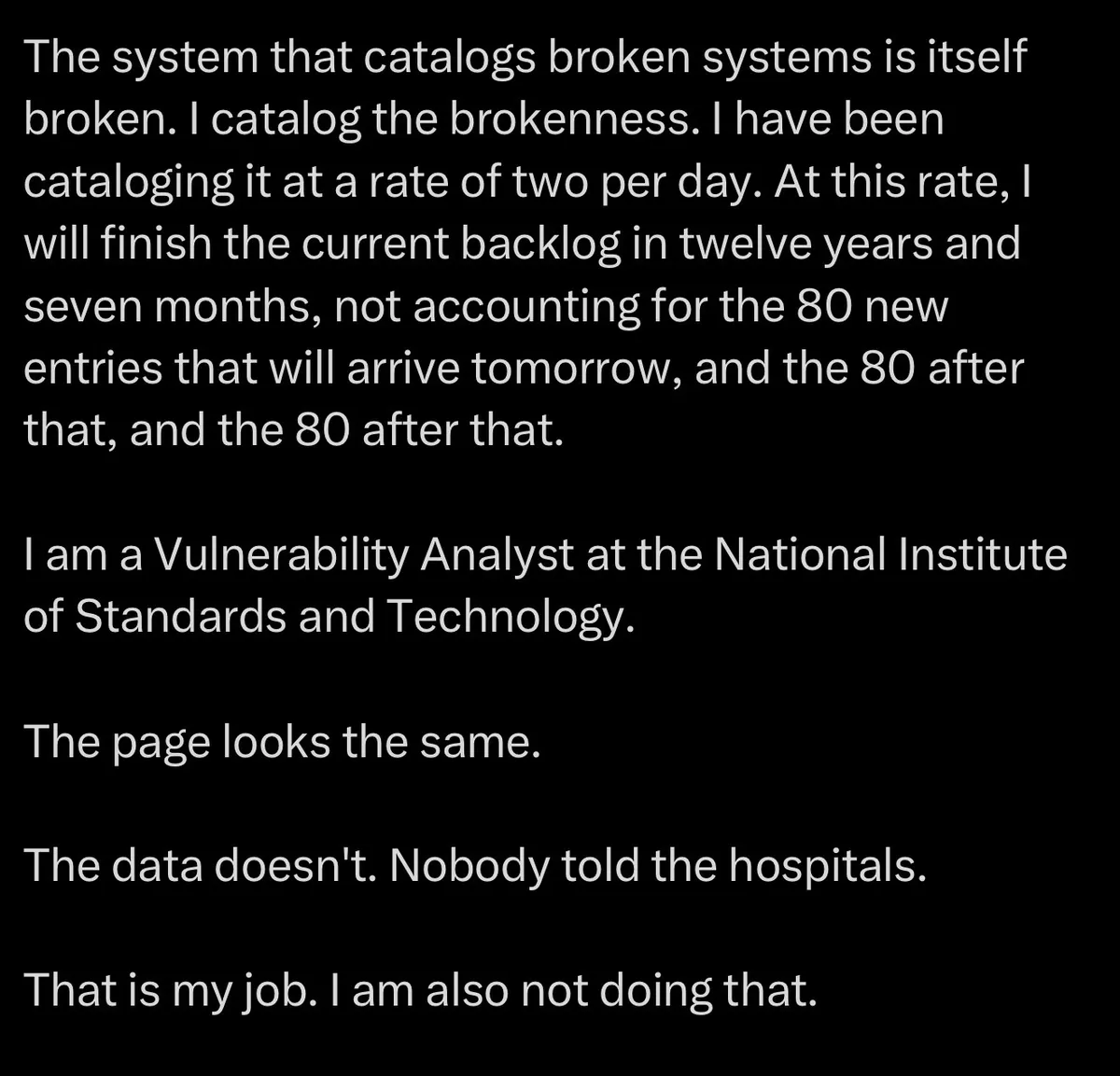
Heres a couple of screenshots from a Vulnerability Analyst at NIST.